To my dear wife
If you are viewing this from the RSS feed: please visit the blog to see the embed. Many RSS readers filter out embed codes.
more ...
If you are viewing this from the RSS feed: please visit the blog to see the embed. Many RSS readers filter out embed codes.
more ...With the motto “better late than never” here are some calls to action:
 I was reading the latest FudSec piece (Generating a False Sense of
Insecurity)
where I found the following statement (emphasis added):
I was reading the latest FudSec piece (Generating a False Sense of
Insecurity)
where I found the following statement (emphasis added):
more ...Facebook now has 300 million users. Let’s assume that each user has at least one piece of user-generated content on their Facebook page cause, well, it’s a ...
WebHostingChoice pretends to be a hosting review site (it contains categories like “best uk web hosting”), however it only seems to be a placeholder for a couple of affiliate links to a limited number of hosts. Their WOT (web of trusts) rating isn’t so great either. While WOT has ...
more ... So, the Microsoft COFEE (Computer Online Forensic Evidence Extractor)
tool was leaked. I took a quick look at it, and – as expected – there is
nothing “magical”, “secret” or “backdoorish” about it (even though I
love the picture which comes with the Gizmodo
article,
the text itself is complete and utter ...
So, the Microsoft COFEE (Computer Online Forensic Evidence Extractor)
tool was leaked. I took a quick look at it, and – as expected – there is
nothing “magical”, “secret” or “backdoorish” about it (even though I
love the picture which comes with the Gizmodo
article,
the text itself is complete and utter ...
 Since its inception VirusTotal has been
used by people to compare different AV products (just in case you don’t
know: VirusTotal is great free service which scans the uploaded file
with 40 AV engines currently and reports back the results). The AV
industry has objected to this practice because ...
Since its inception VirusTotal has been
used by people to compare different AV products (just in case you don’t
know: VirusTotal is great free service which scans the uploaded file
with 40 AV engines currently and reports back the results). The AV
industry has objected to this practice because ...
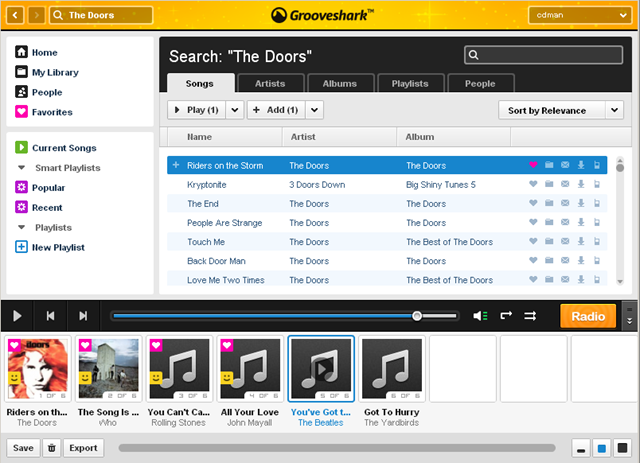
I’ve written about Grooveshark in the past, however I want to mention them again for a couple of reasons:
First of all, they introduced a new user interface, which works great. More than that, you can now seek in the songs! This means that Grooveshark directly addresses three out ...
more ... I’m not a big GDB guy, but Google always
helps:
I’m not a big GDB guy, but Google always
helps:
Create a textfile with the following content:
set height 0
thread apply all bt
detach
quit
Run the following command:
gdb $EXE -pid $PID -command $TEXTFILE > $OUTPUTFILE
where:
 An interesting paper was bought to my attention recently by this blog
post:
The Base Rate Fallacy and its implications for the difficulty of
Intrusion
Detection.
The central question of this paper is: if we have a flow of N packets
per day and our network IDS has a false-positive ...
An interesting paper was bought to my attention recently by this blog
post:
The Base Rate Fallacy and its implications for the difficulty of
Intrusion
Detection.
The central question of this paper is: if we have a flow of N packets
per day and our network IDS has a false-positive ...
Got the links from a friend: